La signature électronique
La première solution de signature en Tunisie

Signer vos documents gratuitement en quelques minutes
Notre application de signature électronique vous fournit une façon simple de signer légalement tous vos documents n'importe quand depuis n'importe quel appareil gratuitement.
En facilitant la signature électronique des documents notre solution élimine la nécessité de processus de signature sur papier lents et coûteux, tout en créant des signatures légales qui fournissent l’intégrité, la confiance et la conformité aux réglementations.

Signer, c'est légal
Faire signer vos documents en ligne n'est pas seulement un gain de temps et d'argent mais c'est aussi légal.
- Notre solution est homologuée par l' Agence Nationale de Certification Electronique et répond à un cadre juridique éprouvé.
- Nos signatures implémentent tous les standards de signatures l'ETSI notamment XAdES, PAdES, CAdES, des signatures qualifiées respectant la loi relative aux échanges et au commerce électronique en Tunisie.
Cadre juridique de la signature électronique en Tunisie
La Tunisie a promulgué une loi sur le commerce électronique : la loi n° 2000-83 du 9 Août 2000, relative aux échanges et au commerce électronique, a défini le certificat électronique et la signature électronique, favorisant un environnement propice au développement des échanges et du commerce électronique, et a permis la création de l’Agence Nationale de Certification Electronique (ANCE) autorité racine de certification électronique en Tunisie, en vue de représenter le plus haut niveau de confiance dans le domaine de la certification électronique, de la sécurité des transactions et des échanges électroniques.
L’Agence Nationale de Certification Electronique (ANCE) a pour principale vocation de sécuriser les échanges électroniques dans divers domaines tels que le e-commerce, l’e-gouvernement, l’e-Banking, l’e-finance, l’e-enseignement ainsi que l’e-santé … Son rôle consiste à sécuriser les transactions de paiement et l’authentification des différents acteurs.
C’est ainsi que toute personne désireuse d’effectuer une opération de paiement sur un site sécurisé par un certificat de l’Agence Nationale de Certification Electronique peut être sûre qu’elle s’adresse à un site fiable et que toutes les données qu’elle communique sont sécurisées. Les principales autres missions de l’ANCE consistent à :
- Etablir des accords de reconnaissance mutuelle avec les Autorités de Certification étrangères.
- Gérer les certificats électroniques (génération, révocation, publication et conservation de certificats).
- Octroyer des autorisations d’activité de fournisseur de services de certification électronique.
- Définir les caractéristiques techniques des dispositifs de signature et de vérification de signature.
- Effectuer l’homologation des systèmes de cryptage.
L’ANCE délivre essentiellement deux types de certificats électroniques :
- Certificat de signature : qui permet d’associer l’identité d’une personne à une clé publique. Il peut être utilisé pour signer, crypter des messages électroniques et s’authentifier lors d’une session sécurisée, comme par exemple lors de la consultation de son compte bancaire, télé déclaration fiscale, CNSS, CNRPS, CCP net, et déclaration douanière, etc….
- Certificat serveur : Il associe l’identité d’un serveur web à une clé publique. Il permet la sécurisation des échanges entre le serveur et ses clients lors de l’établissement d’une session sécurisée par exemple pour l’achat ou le paiement en ligne sur un site marchand.
FAQ sur la signature électronique

Qu’est-ce que une signature électronique?
Une signature manuscrite consiste à apposer une marque
personnelle sur un document papier. Elle exprime la volonté du
signataire et son accord par rapport au contenu du document.
Transposée dans le monde électronique, la signature électronique
a la même valeur légale que la signature manuscrite.
La
signature électronique est formée de trois composantes :
- Le document porteur de la signature.
- La signature elle-même.
- Le certificat électronique authentifiant le signataire .
La signature électronique est-elle visible sur le document signé ?
La signature électronique se différencie de la signature écrite par le fait qu’elle n’est pas visuelle mais correspond à un nombre ou une suite de nombres.
En effet, l’action de signer numériquement produit une
information binaire appelée communément signature électronique.
Un document peut contenir plusieurs signatures électroniques.
Quels types de fichiers peuvent être signés électroniquement ?
Tous types de fichiers sans exception peuvent être signés (documents Word, PDF, XML, etc.). Le format de fichier le plus utilisé est le PDF, pour sa portabilité et aussi la possibilité d’apposer plusieurs signatures électroniques. Mais également les fichiers XML normés pour les échanges entre les entités publiques.
A quoi sert la signature électronique ?
Tout comme les signatures manuscrites, les signatures
électroniques sont utilisées pour identifier les co-signataires
(auteurs) des données électroniques (un email par exemple).
Les signatures électroniques permettent de garantir les
propriétés de sécurité suivantes:
- Authentification : la vérification de l'identité d'une personne (ou d'un hôte : serveur et client). Cela garantit l'identité de la personne qui a signé les données : l'origine du message, du document ou de la transaction est incontestable.
- Confidentialité et Intégrité des données : la signature électronique protège l'intégrité des données. Cela signifie que le document reçu n'a pas été altéré, volontairement ou involontairement. Dans le cas contraire, le document est signalé comme ayant été modifié.
- Non-répudiation : le signataire d'un document prouve son identité. La non-répudiation établit, plus tard, qui a participé à une transaction. L'expéditeur ne peut nier avoir envoyé le message et le destinataire ne peut nier l'avoir reçu. Simplement, la non-répudiation signifie qu'une information ne peut être rejetée, tout comme avec les signatures manuscrites.
Les signatures électroniques sont créées et vérifiées grâce aux certificats électroniques.
Qu’est-ce qu’un certificat électronique ?
Un certificat électronique est un document sous forme électronique qui a pour but d’authentifier l’identité de la personne signataire : c’est la carte d’identité du monde électronique.
Que contient un certificat électronique ?
Les informations contenues dans le certificat électronique sont
les suivantes :
- Le nom du porteur du certificat.
- La date de début de validité du certificat.
- L’organisation à laquelle appartient le porteur (si nécessaire).
- L’adresse où trouver les listes de certificats révoqués (LCR).
- Le nom de l’entreprise de confiance, c’est-à-dire de l’autorité qui a émis ce certificat électronique.
- La signature de cette autorité sur ce certificat.
- Eventuellement la photographie du porteur ou du logo de l’entreprise.
- etc…
Le certificat électronique est divisé en deux parties :
- La première partie contient les informations.
- La deuxième partie contient la signature de l’autorité qui a délivré le certificat.
Qui délivre le certificat électronique ?
Le certificat électronique doit être délivré par une autorité de
certification (AC) qui est un organisme reconnu comme étant
compétent pour délivrer des certificats à une population auprès
de laquelle elle a toute confiance et en assurer la validité.
Elle s'engage sur l'identité d'une personne au travers du
certificat électronique qu'elle lui remet.
Une autorité de
certification est responsable (vis-à-vis de ses clients, mais
aussi de toute personne se fiant à un certificat électronique
qu'elle a émis) de l'ensemble du processus de certification et,
par voie de conséquence, de la validité des certificats qu'elle
émet. Par ailleurs, c’est elle qui définit la politique de
certification et la fait appliquer.
Une autorité
de certification s'organise autour de trois fonctions
fondamentales :
- Fonction d'organisation : traitement des demandes de certificats, contrôles des informations, validation ou rejet des demandes, révocation des certificats.
- Fonction technique : responsable de la production des certificats électroniques, environnement sécurisé de bout en bout.
- Fonction de distribution des certificats
Comment signer un document ?
Lorsque vous signez un document, le logiciel de signature en crée
une empreinte numérique, appelée hachage : sorte de condensé
numérique composé d’une suite de lettres et de chiffres.
Le
hachage est unique (la plus petite modification du document
produira un hachage différent). Ce hachage est ensuite chiffré
(codé) grâce à la clé privée de votre certificat numérique. Le
hachage chiffré et la clé publique sont réunis pour composer la
signature numérique, annexée au document.
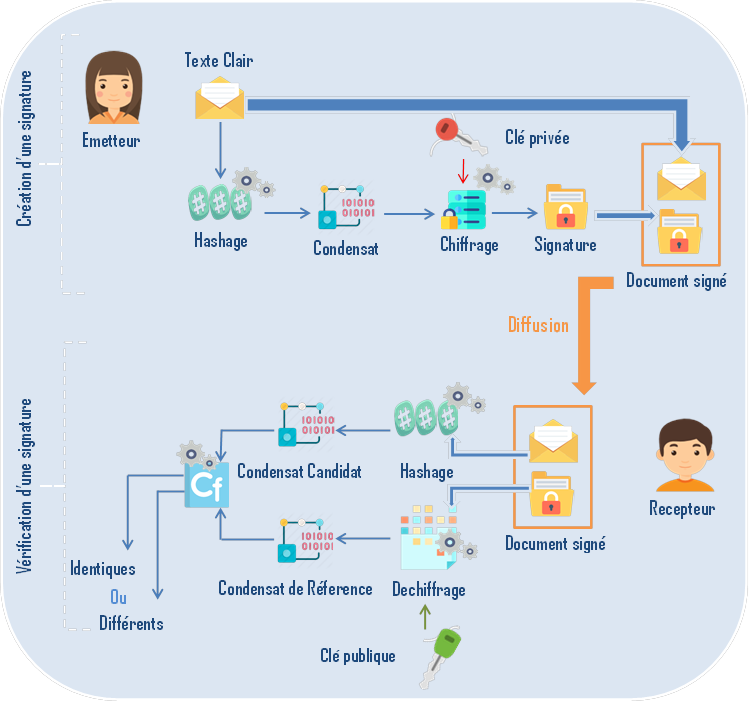
Comment vérifier une signature ?
Lorsque le document signé est ouvert, le hachage est déchiffré
grâce à la clé publique du signataire. Puis le logiciel de
vérification recalcule le hachage du document : si celui-ci est
identique au hachage déchiffré auparavant, le document n’a pas
été modifié. Le logiciel affiche alors un message certifiant son
intégrité, ainsi que le nom du signataire.
Donc le
principe de la signature électronique repose sur deux familles
d’algorithmes, qui seront utilisés de manière complémentaire :
Il est fortement recommandé d’associer un horodatage à chaque signature électronique.
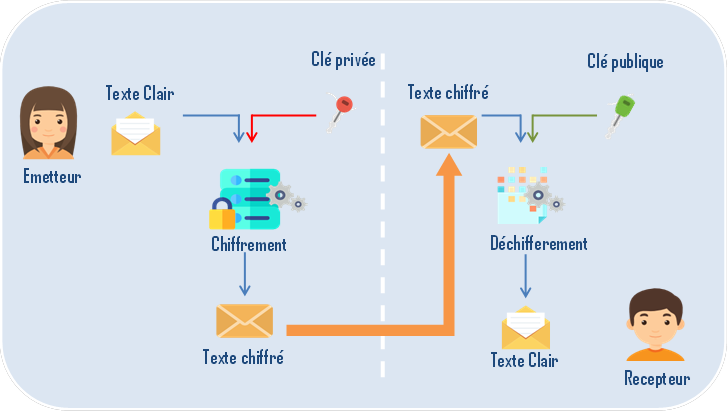
C'est quoi un algorithme de chiffrement symètrique ?
Le principe d’un algorithme asymétrique est simple.
Un couple de clefs numériques est construit de manière à ce que le cryptogramme (texte crypté) généré à partir d’un texte clair et l’une des clefs ne puisse être aisément retrouvé qu’avec l’autre clef.
En pratique, l’une des clefs est conservée secrètement : clef privée, tandis que l’autre est diffusée publiquement : clef publique.
Seul le propriétaire d’une clef privée (l’émetteur dans notre exemple) aura pu chiffrer un texte déchiffré avec la clef publique associée.
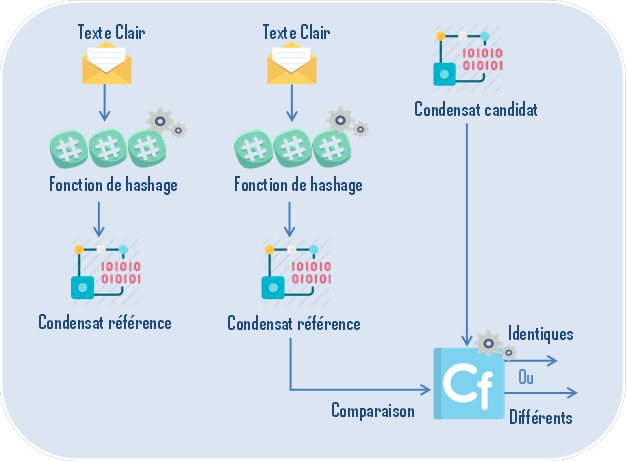
C'est quoi une fonction de hachage ?
Est une fonction à sens unique et sans collision qui permet de calculer une empreinte (ou condensat) de taille fixe à partir des données fournies de tailles variables. Ces fonctions sont dites à sens unique car il est impossible de retrouver les données initiales à partir de l’empreinte.
Une fonction est dite sans collision ou injective lorsqu’il est
réputé très difficile de trouver deux sources différentes
conduisant à un même résultat.
Le calcul du condensat d’un
document et la comparaison de celui-ci avec sa valeur initiale
permet de contrôler l’intégrité d’un document.
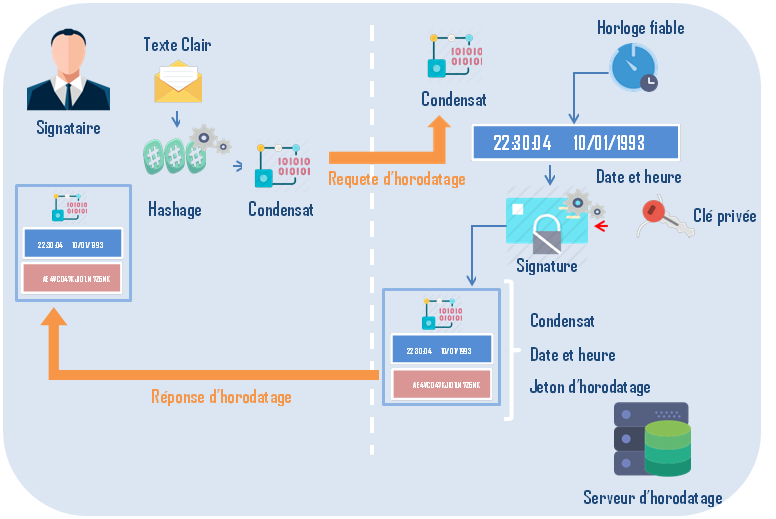
C’est quoi l’horodatage électronique ?
Nombreuses sont les procédures administratives qui mettent en jeu la date d’envoi des documents : dépôt de candidatures, réponses à des appels d’offres, déclarations diverses, etc. Les mécanismes traditionnels utilisent le cachet de la poste.
La dématérialisation de telles procédures passe par un équivalent électronique à ce cachet de la poste.
Le format PKCS#7 qui décrit les conteneurs de données signées dans la messagerie électronique inclut un champ pour indiquer la date à laquelle le message a été signé.
C’est toutefois la date et l’heure du poste de travail du signataire qui sont utilisés dans ce champ.
L’émetteur peut donc tricher en indiquant des dates fausses.
De la même façon, un tiers mal intentionné ayant récupéré une clé privée associée à un certificat périmé peut ramener artificiellement la date de sa machine dans la période de validité du certificat et émettre des documents signés.
La signature électronique d’un document est donc indissociable d’un mécanisme qui garantit que le document existait à une date et une heure donnée et n’a pas été altéré depuis. C’est l’horodatage.
Il consiste à transmettre à une autorité de confiance, appelée autorité d’horodatage, une requête comprenant le condensat du document à horodater.
L’autorité renvoie au demandeur un jeton d’horodatage, le
condensat, une date et une heure, le tout signé par l’autorité
d’horodatage.
